Developing a security policy
A security policy is extremely important for companies and organizations as it outlines the various security threats that face the company and it’s assets and outlines the strategies to be implemented to mitigate these threats.
What is a security policy?
A security policy is a set of rules that outlines the practices to be followed to protect an organization and it’s servers from threats. It clearly defines the organization’s assets and the risk factors affecting those assets. Given the dynamic nature of the companies assets and what is important, the security policy must be updated when any changes are made to the company’s assets or infrastructure.
In this particular case, our primary asset is the server. The primary outline when developing a security policy is the CIA triage (Confidentiality, integrity, and availability).
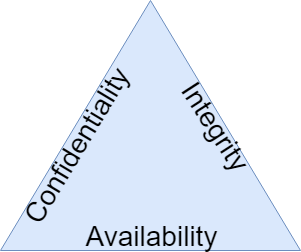
As shown in the figure, It gives us an understanding of the 3 important factors we must take into account when securing a server or any system for that matter.
- Confidentiality – The confidentiality of the data, we must make sure that only authorized personnel can access the server and the data.
- Integrity – The integrity of the system and the data. The system should not vulnerable to any exploits and data on the server cannot be changed or manipulated without authorization.
- Availability – The system is online and available at all times. The system should be secure and protected from DDoS attacks, ensuring that the data is available and accessible to those who need it.
Developing the security policy for our server
When developing a security policy, it is important to make it as simple and as effective as possible, the more security in place the more intrusive it becomes.
A good security policy for our server will be based on the CIA triage as explained previously and will include various security measures and techniques that we looked at briefly in the security on-premises and security in the cloud sections.
Let us imagine we want to create a security policy for our single Linux server that runs a web application. We will be creating a simple security policy that will accommodate all aspects of security based on the following keys of importance.
- Access to the system
- Server Security
- Backups and recovery
Access to the system
- User authentication and password policies
Protection Policies
-
- Passwords should be more than 8 characters and contain special symbols and characters. This will prevent passwords from being guessed by attackers.
- When using SSH, SSH keys are preferred as they eliminate brute force attacks as a potential vector for an attacker.
- Users should not use the same password for other accounts. This will help prevent company security from being linked with the security of accounts that belong to the employee.
- Passwords should not be written down or shared through any electronic communication medium like emails and instant messaging services. This will prevent phishing attacks on employees as they will not be coerced into sending passwords via any electronic medium.
- Always store your passwords in password managers with encryption. This will prevent employees from forgetting their passwords and protect them from being accessed at the same time.
- Take backups of your SSH keys. This will prevent accidental deletion or loss of the keys as they can be restored.
- Do not store your SSH keys on any cloud storage provider. This prevents any SSH keys from being linked or stored on any online platform that could be compromised.
Change policies
-
- All users must change their passwords on a regular basis. At least once a month. This will reduce the chances of attackers guessing passwords, or using older passwords.
- All inactive users on a system should be deleted. This will prevent previous employees with unauthorized access from regaining access to the servers or systems.
Server security
Protection Policies
-
- Only authorized personnel can interact with the server. This mitigates unauthorized personnel from accessing or interacting with the server and creates a system of accountability.
- All servers should be kept updated and patched regularly. This keeps the systems up to date with the latest security patches in the event of a software vulnerability.
- All unused or inactive services and ports should be closed. This reduces the attack surface for attackers and limits their activity and interaction with other ports.
- All activity on the server should be logged. This creates a system of accountability where all user activity is logged and analyzed.
- Root access should be avoided unless necessary. This prevents any modification of the system by unauthorized personnel. It also helps prevent root level mistakes, that cannot be reversed.
Backups and recovery
Protection Policies
-
- Backups should be taken daily, and stored for a period of a month. This provides a very reliable system of backups and security.
- Database backups should be taken weekly and redundant backups should be taken monthly and stored for a period of 1 year. This ensures that backups are also kept safe and maintained for a year for the historical records.
We have created our simple but effective security policy for our servers, we will now begin implementing them in the next section.


